Teleport Blog
Subscribe to the RSS FeedFeatured Post
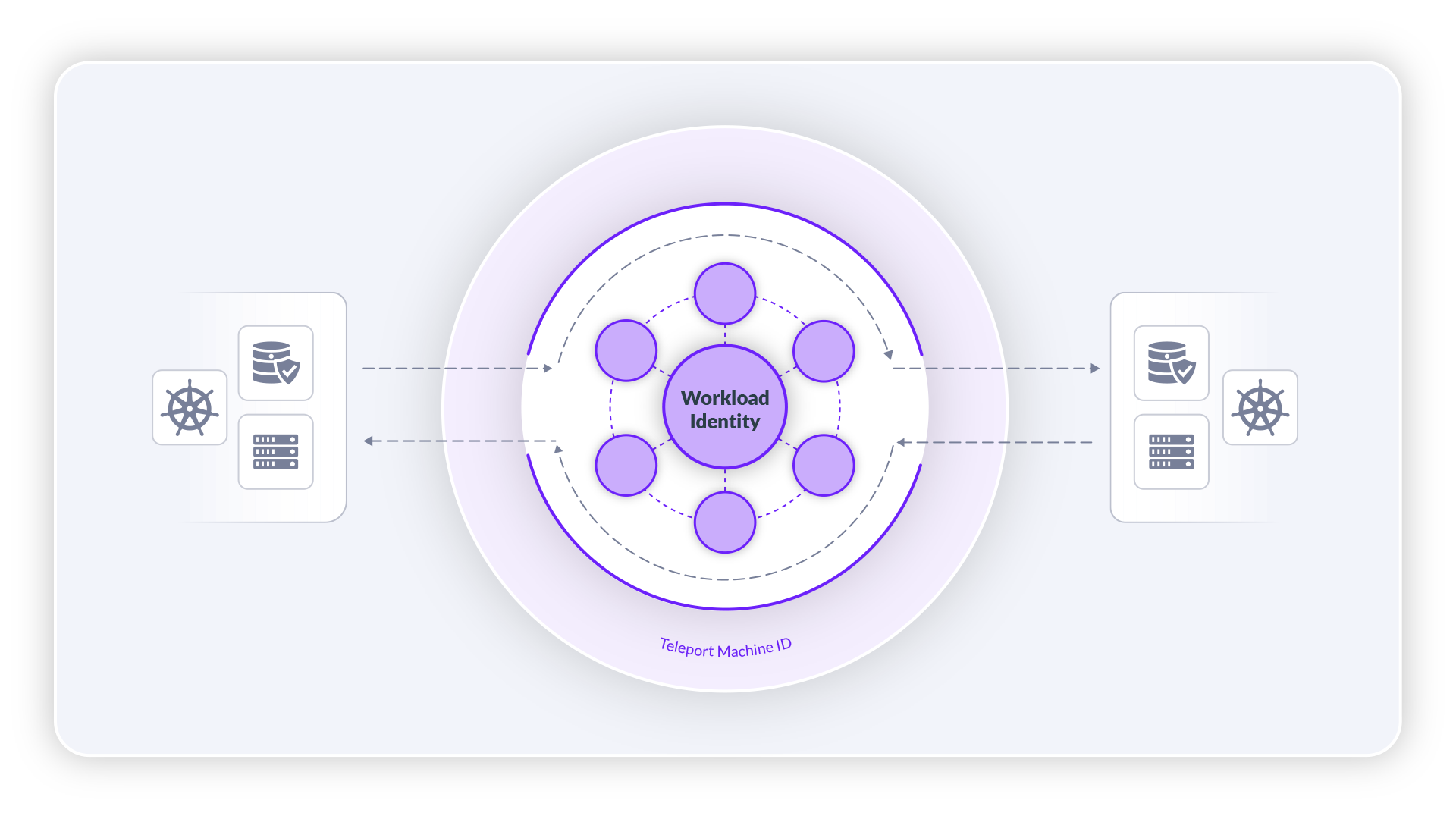
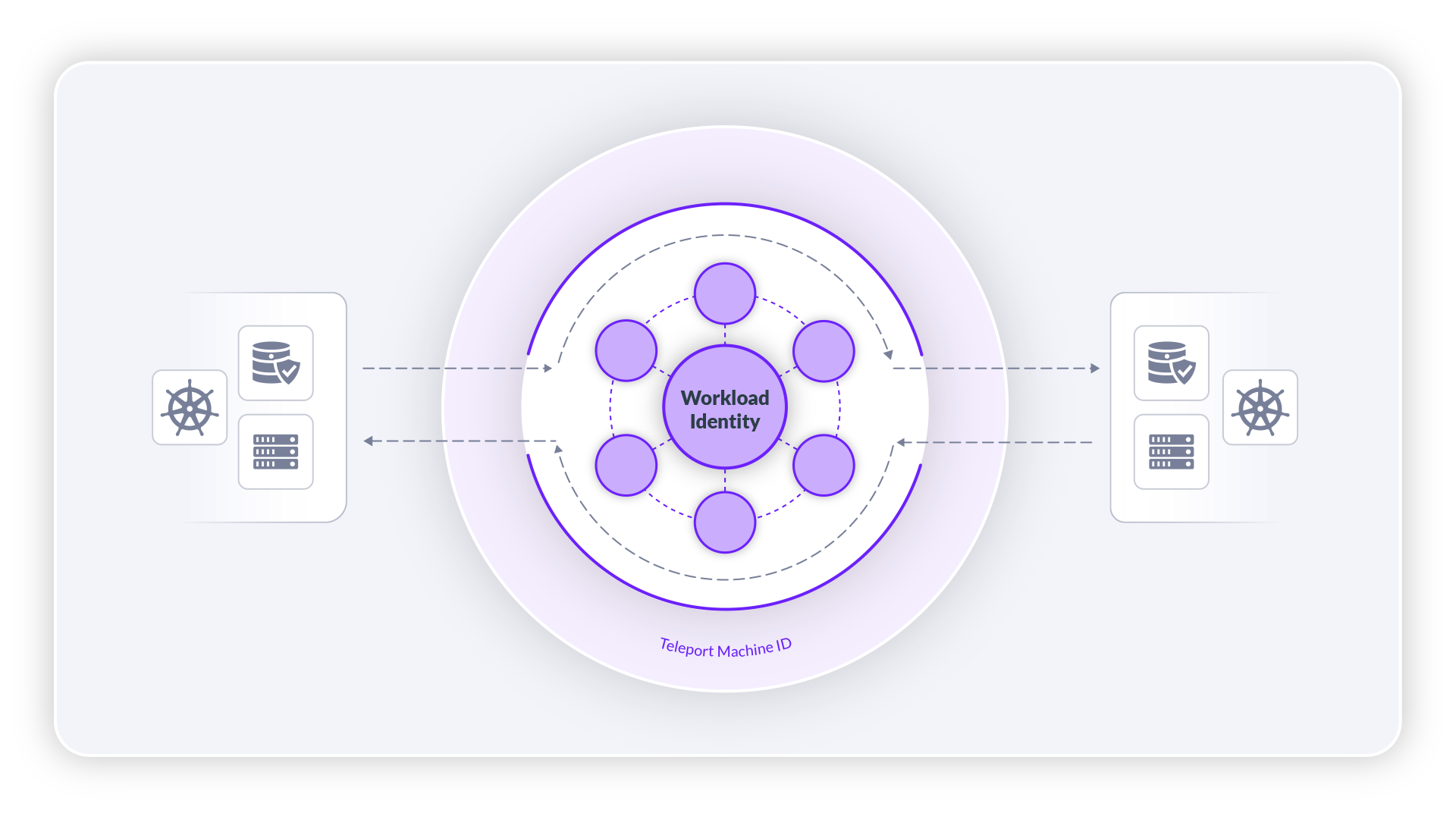
Teleport Workload Identity
An introduction to the preview feature Teleport Workload Identity. A feature that lets teams bootstrap and issue identities to services across heterogeneous environments and organizational boundaries.
Oss
Teleport Community Edition will restrict commercial usage starting with version 16
A detailed explanation, schedule, and FAQ on why we have switched Teleport Community Edition to a commercial software license.
Announcements
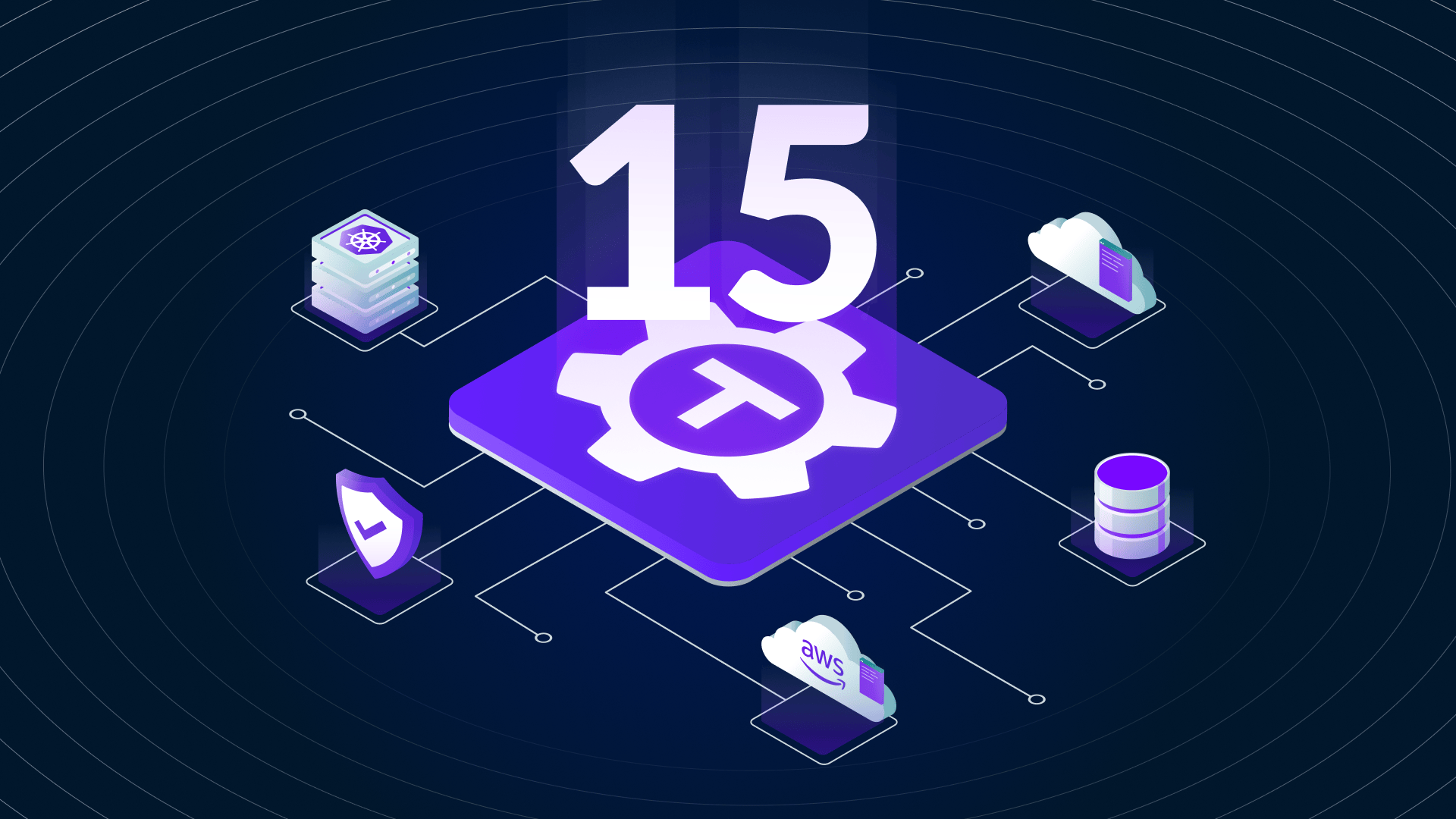
Teleport 15
Teleport 15 introduces significant enhancements, including a revamped UI, better session playback, extended AWS KMS support, and a standalone Kubernetes Operator, and much more.
AWS
Connect Using EC2 Instance Connect via Teleport
This post describes a new Teleport feature that enables SSH access using the EC2 Instance Connect Endpoint.
Articles by topic
- All
- AWS
- RBAC
- access-requests
- announcements
- applications
- audit
- bastion
- certificates
- company
- compliance
- cybersecurity
- databases
- device-trust
- engineering
- featured
- governance
- gravity
- kubecon
- kubernetes
- machine-id
- mongodb
- newsletter
- okta
- oss
- pam
- passwordless
- postgres
- programming
- saml
- security
- snowflake
- ssh
- sso
- teleport
- terraform
- vpn
- webauthn
- windows
- z3
- zero-trust
Blog Posts

Subscribe to our newsletter